Topic(s)
Security
Author(s)
For these movie events, we always tailor the presentation towards the movie that we have paired that talk with. In putting together the content for this year’s session, I realized that the Star Wars saga really is a lesson in what not to do with a Cybersecurity strategy!
Case Study – The Empire
The Empire is terrible at evolving security strategies. It’s bad enough that after the destruction of the first Death Star, their big follow up plan was to just build the thing again – and then the New Order decided that the third time must be the charm because they built an even bigger Death Star (yeah, they called it Star Killer Base, but c’mon, we all know it was really Death Star #3). We could almost forgive The Empire for basically having only 1 plan to rule the universe – if they learned from their mistakes and didn’t build the things with essentially the same vulnerability every single time!
So what lessons in Cybersecurity can we learn from The Empire’s Death Star defeats? Let’s take a look.
Death Star #1

While it may have been a weapon of galactic terror designed to bring the Universe to its knees, The Empire made the simple mistake of allowing their security plans to be compromised, stolen, and broadcast online. Those plans revealed that the Death Star had a vulnerability engineered by a 3rd party contractor. This vulnerability was unknown to the owners, and therefore it hadn’t been patched.
With knowledge of the system’s vulnerability, skilled hackers evaded the standard security tools (lasers and spaceships) and exploited that vulnerability, detonating the system’s core by shooting a few torpedoes through an exhaust port.
Result = Boom.
Death Star #2

Construction on The Empire’s second planet-destroying weapon ran behind schedule. As such, the IT department had not yet fully deployed the defenses for the environment, leaving it vulnerable. Yes, there were some security measures in place, but they were obviously insufficient.
Looking deeper into the destruction of the 2nd Death Star, you will discover that The Empire’s employees weren’t trained to recognize a phishing attack. This allowed the Rebels to use social engineering to talk their way onto an Empire-run landing pad using little more than an out-of-date security code.
Once they had gained entry, these Rebel hackers disguised themselves as Empire soldiers so they could compromise a remote resource responsible for protecting the station.
With this layer of security compromised, it was relatively easy to fly right in and detonate the core.
Result = Boom.
Death Star #3 (Star Killer Base)

A disgruntled employee of The Empire (they've been rebranded “The New Order”, but it’s really The Empire with a new logo and marketing campaign) quit his job and takes with him confidential company data. That data falls into the wrong hands and before you know it, a plan to attack the base is underway.
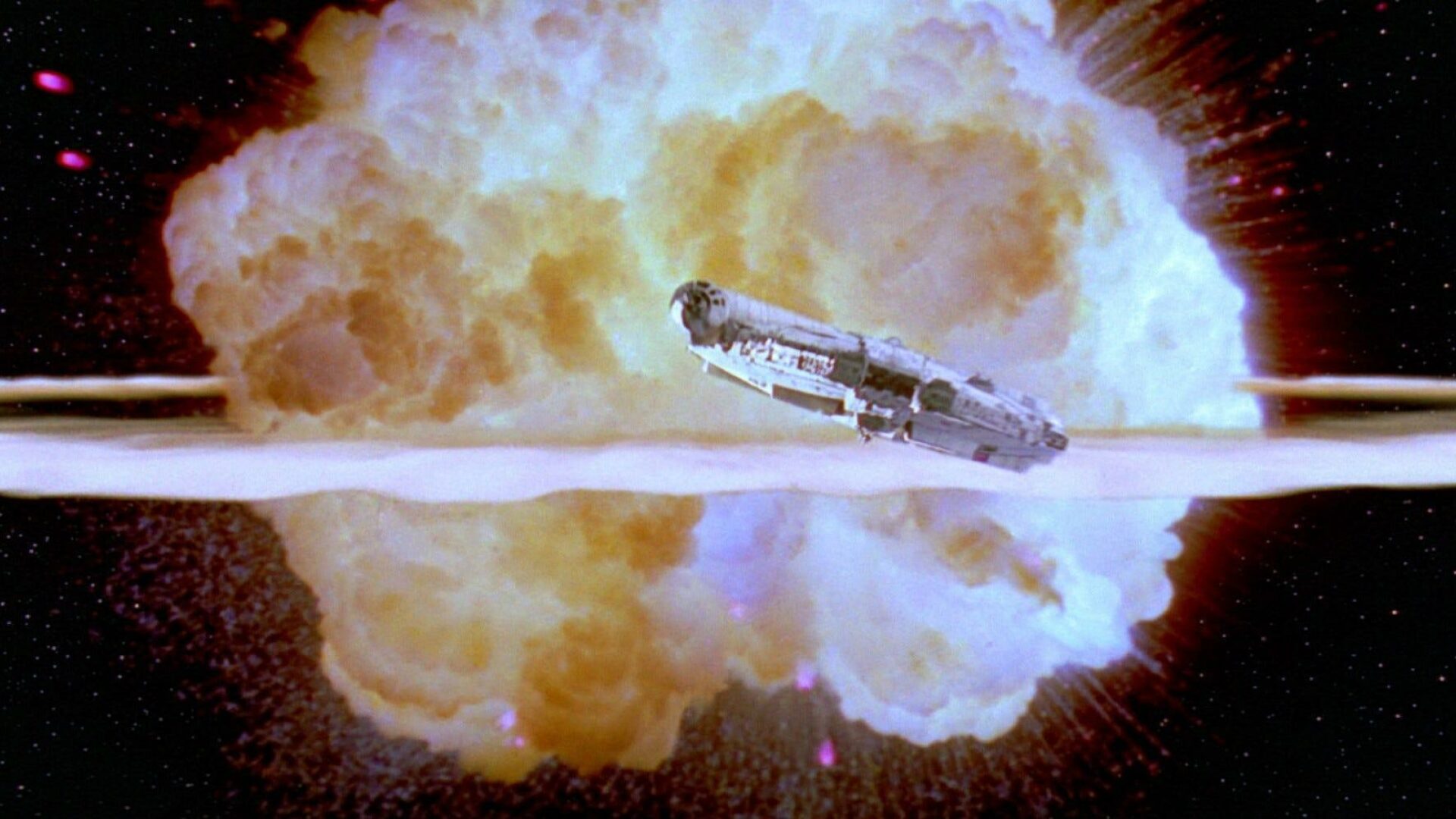
The Millennium Falcon exploits the fact that The Empire is using only a conventional pattern recognition system and makes it inside the secured environment by mimicking traffic that would normally be ignored.
Once inside, another employee is compromised and forced to drop the system’s shields, making it easy for attack fighters to destroy the system’s oscillator (which is the new name for the “core” – that's right, all 3 Death Stars were destroyed by the same general flaw in their design).
Once again…boom.
Don’t Be The Empire
Look at your own environment and security strategy. Are you vulnerable in the same ways that have doomed The Empire?
- Are your employees prepared for a cyberattack? Do they know how to recognize phishing emails or how to respond when a system is compromised?
- Can employees leave your organization and take sensitive data with them? What about devices that may be lost or stolen – what happens to that data?
- Does your infrastructure include elements developed or managed by 3rd party contractors who may have unknowingly introduced vulnerabilities into your systems? Has anyone outside of your organization (and those 3rd party contractors) audited those systems for security flaws?
- Are you only using the standard security tools and detection solutions to monitor your security?
These are just some of the Cybersecurity failures that contributed to The Empire’s fall – but truthfully, these failures are not unique to a galaxy far, far away. Many of the companies we work with on their Cybersecurity strategies face these same challenges. If your organization does too, we can help.
Contact Envision's Cybersecurity experts today and allow us to schedule a meeting to review your cyber strategy. We know everyone is busy, so we promise to keep the meeting to just 45 minutes. To make sure that we touch on the right points during that focused meeting, we will start with a 5-minute call in advance so we can identify exactly what your concerns are. We will then customize the meeting to your needs, including bringing along the right resources or partners so you don’t have to sit through 5 meetings just to get to a solution!
Remember, a lone Jedi can’t defend the entire galaxy, nor can you be the sole resource on the battlefront of a modern Cybersecurity war. Your personal data is at risk, your company’s future is at risk, and your reputation as an IT professional is at risk. Whatever you are doing today, you have to do more. Contact us today and let us help you with that.
Explore our cybersecurity services to find out how you can further protect your organization and its people.